ARTIKEL POPULAR
- Google Quantum AI released a white paper on Tuesday, warning that crypto wallet encryption could be cracked in nine minutes.
- The whitepaper shows a 20-fold improvement in the efficiency of crypto wallet cracking.
- Roughly 1.7 million dormant Bitcoins from the Satoshi era and 20.5 million ETH are at “at-rest” risk.
Google Quantum AI released a white paper on Tuesday, warning the cryptocurrency industry about threats that could crack encrypted wallets in less than 10 minutes under advanced quantum scenarios. The updated quantum resources from Google show a 20-fold improvement in the efficiency of cracking wallet encryption, putting roughly 1.7 million dormant Bitcoin (BTC) and 20.5 million dormant Ethereum (ETH) at risk.
Google flags how quantum could break crypto wallet encryption in under 10 minutes
Google’s division of quantum computing technologies, Google Quantum AI, released a white paper called “Safeguarding cryptocurrency by disclosing quantum vulnerabilities responsibly” on Tuesday, which is basically a warning to the cryptocurrency industry against quantum computing. The paper reveals that fast-clock Cryptographically Relevant Quantum Computers (CRQCs) can bypass the 256-bit Elliptic Curve Cryptography (ECC) encryption.
Given that these CQRCs are in a primed state, where the first half of Shor’s algorithm is precomputed, the time required to crack the encryption reduces to 9 to 12 minutes under certain threat scenarios.
Types of Quantum computers and threats
CRQCs' hardware could be a fast clock using superconducting or photonic machines for time-restricted decryption, or a slow clock using a neutral-atom or ion trap to threaten dormant wallets.
The attacks are mainly divided into three types: “at-rest attacks,” which target long-exposed public keys in dormant or reused wallets, “on-spend attacks,” which intercept a transaction and break the key before the block is mined, and “on-setup attacks,” which create reusable backdoors in a protocol.
Quantum threat to dormant Bitcoin and Ethereum
The slow-clock CQRCs pose a threat to Bitcoin’s fragmented security history, including the 2021 Taproot (P2TR) upgrade, which brought advanced features but abandoned the practice of hiding public keys behind hashes. This has made modern and Satoshi-era addresses vulnerable, putting over 1.7 million BTC in "Satoshi-era" addresses and a total of 2.3 million dormant BTC vulnerable to at-rest attacks.
In the case of Ethereum, the programmable logic executed through smart contracts and the multiple layers of Decentralized Applications (dApps) create a larger attack surface. These include Account Vulnerability, which targets 20.5 million ETH with exposed public keys, Admin Vulnerability, Code Vulnerability, Consensus Vulnerability, and Data Availability Vulnerability.
According to the paper, "The community will soon face difficult, unprecedented decisions regarding the fate of these assets, forcing tradeoffs between the immutability of cryptographic property rights and the economic stability of the network."
The paper urges the cryptocurrency industry to make a complete transition to Post-Quantum Cryptography (PQC) as multiple analysts believe the Quantum-day, when quantum computers will break blockchain encryption, could be as early as 2032.
According to Justin Drake, a researcher at the Ethereum Foundation, “There's at least a 10% chance that by 2032 a quantum computer recovers a secp256k1 ECDSA private key from an exposed public key.”
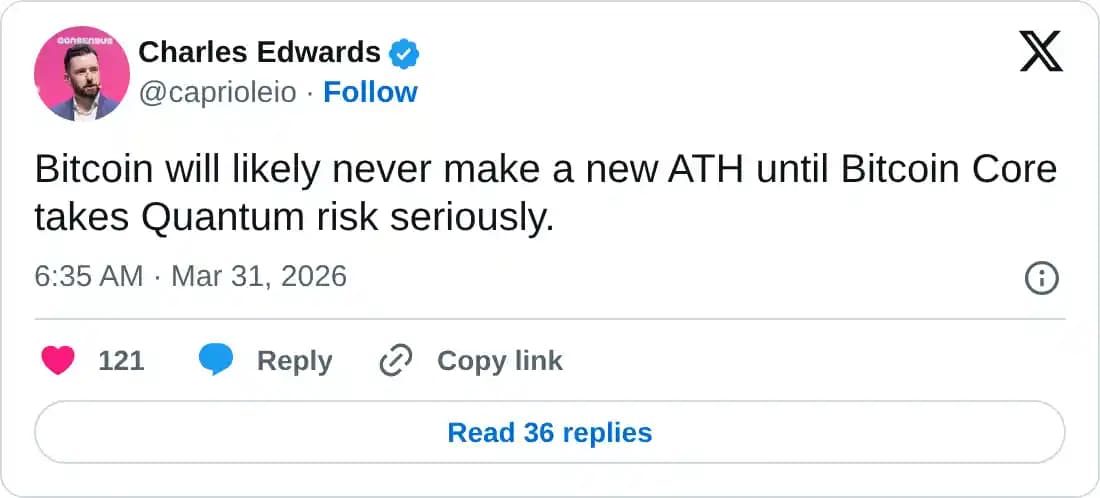
Meanwhile, Charles Edwards, the founder of Capriole Investments, has shared on X that the odds of Q-day by 2032 have reached 85% and that “Bitcoin will likely never make a new ATH until Bitcoin Core takes Quantum risk seriously.”
Need of the decade: Post-quantum measures
Bitcoin’s BIP-360 request plans to replace Taproot’s key path option with Pay-to-Merkle-Root (P2MR) to minimize elliptic curve exposure. This reduced exposure of the public key would be the initial step toward a cryptographic overhaul to address the quantum threat.
On the other hand, the Ethereum Foundation's roadmap outlines a four-fork plan (I, J, L, and M forks) as part of its quantum security measures, which could be in effect starting in 2029. The names are yet to be determined, but the initial I is likely to introduce quantum-secure public keys, J could roll out quantum-safe signatures, L could release quantum-resistant zero-knowledge proofs, and M would extend these features to Layer-2.
Considering Ethereum is leading the real-world asset tokenization and other major DeFi narratives, a threat to its blockchain network could derail the on-chain shift of the traditional financial market.
Putting it all together, the quantum threat is closer than anticipated, and Google's white paper could kick off the race for Post-Quantum Cryptography (PQC), shifting core teams away from functionality features.